NIS2 and Related Regulations: A Holistic View for OT/ICS Teams
Critical Entities Resilience (CER) Directive:
Relevance to OT/ICS Teams
The CER Directive works alongside NIS2 by targeting risks to physical infrastructure—like power disruptions, sabotage, or extreme weather events. While NIS2 focuses on digital threats, CER ensures that your physical systems and operational processes are also resilient.
What You Need to Know
As of October 2024, national authorities started identifying critical entities and reviewing their risk management processes. This means your physical and cyber resilience plans will go under review—including how you protect OT environments, maintain uptime, and coordinate emergency response. Expect increased collaboration with regulators and a push to integrate physical and cyber risk strategies.
EU Cyber Resilience Act (ECRA):
Relevance to OT/ICS Teams
The ECRA transitioned into law in December 2024 and introduces mandatory cybersecurity requirements for any products with digital components. This includes OT systems, industrial devices, and embedded software.
What You Need to Know
Enforcement starts in December 2027—but you should start reviewing your digital supply chain now. The ECRA demands secure-by-design product development, vulnerability management, and ongoing support from vendors. This means tighter vetting of device manufacturers and stronger supply chain oversight for components running in critical ICS environments.
ENISA NIS360 2024 Report: What OT/ICS Data Reveals
The ENISA NIS360 2024 assesses the maturity and criticality of sectors deemed highly critical under the NIS2 directive. Equipped with data from within the scope sectors and insights from Eurostat, the goal of this analysis is to assist member states and national authorities in uncovering gaps and prioritizing efforts.
Insight 1: Cybersecurity Maturity Levels Are Mixed
The report reveals that electricity ranks among the most mature sectors due to targeted regulations like the Network Code on Cybersecurity. Other critical infrastructure sectors lag significantly behind.
Gas, oil, district heating and cooling, and hydrogen subsectors show considerably lower maturity levels, with entities struggling particularly with legacy OT systems integration and post-incident response capabilities. Maritime transport also faces similar challenges with outdated OT systems making it vulnerable to cyberattacks, despite its vital role in global trade. This disparity highlights that regulatory frameworks and sector-specific guidance are crucial drivers of cybersecurity maturity in OT environments.
Insight 2: Two OT/ICS Sectors Are in the Risk Zone
The following highly critical sectors are in the risk zone: Maritime and gas. Based on the report, here is what each sector should focus on.
Maritime
- Prioritize OT vulnerability assessments
- Implement secure-by-design principles for new deployments or upgrades
- Develop and test your incident response plans for cross-border incidents
Gas
- Strengthen post-incident response plans and test them regularly
- Collaborate with electricity and manufacturing sectors
- Focus on securing the supply chain
NIS2 Compliance Requirements: An OT/ICS Implementation Guide
Duty to Provide Entity Contact Details:
- Action: Ensure accurate and up-to-date contact information is registered with ENISA.
- Tactics: Designate a primary point of contact for NIS2 communications within your OT/ICS security team. Establish a process for updating changes within three months. Foreign corporations providing services in the EU must designate a representative.
Reporting Obligations for a Potential Severe Incident:
NIS2 places significant emphasis on rapid and effective incident reporting, with tight deadlines and potential sanctions for non-compliance. This is a critical area for OT/ICS, where incidents can have cascading physical and economic impacts.
What Constitutes a "Severe Incident" for OT/ICS:
- Severely impacting operational services.
- Imposing significant financial loss (for example, production downtime, equipment damage).
- Significant immaterial or material impact on personnel or the entity itself.
Supervision, Enforcement, Fines, and Penalties: The Stakes for OT/ICS
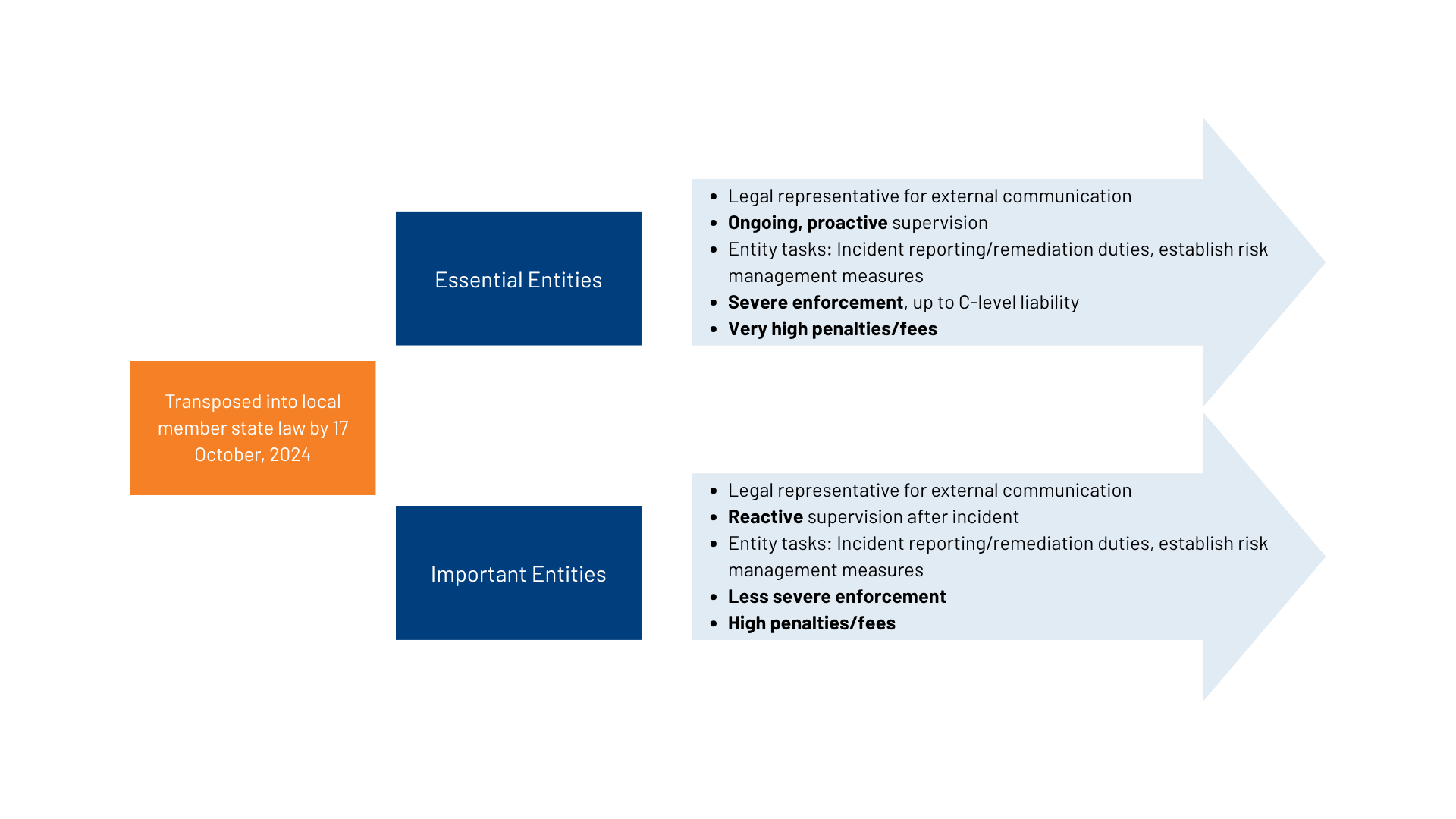
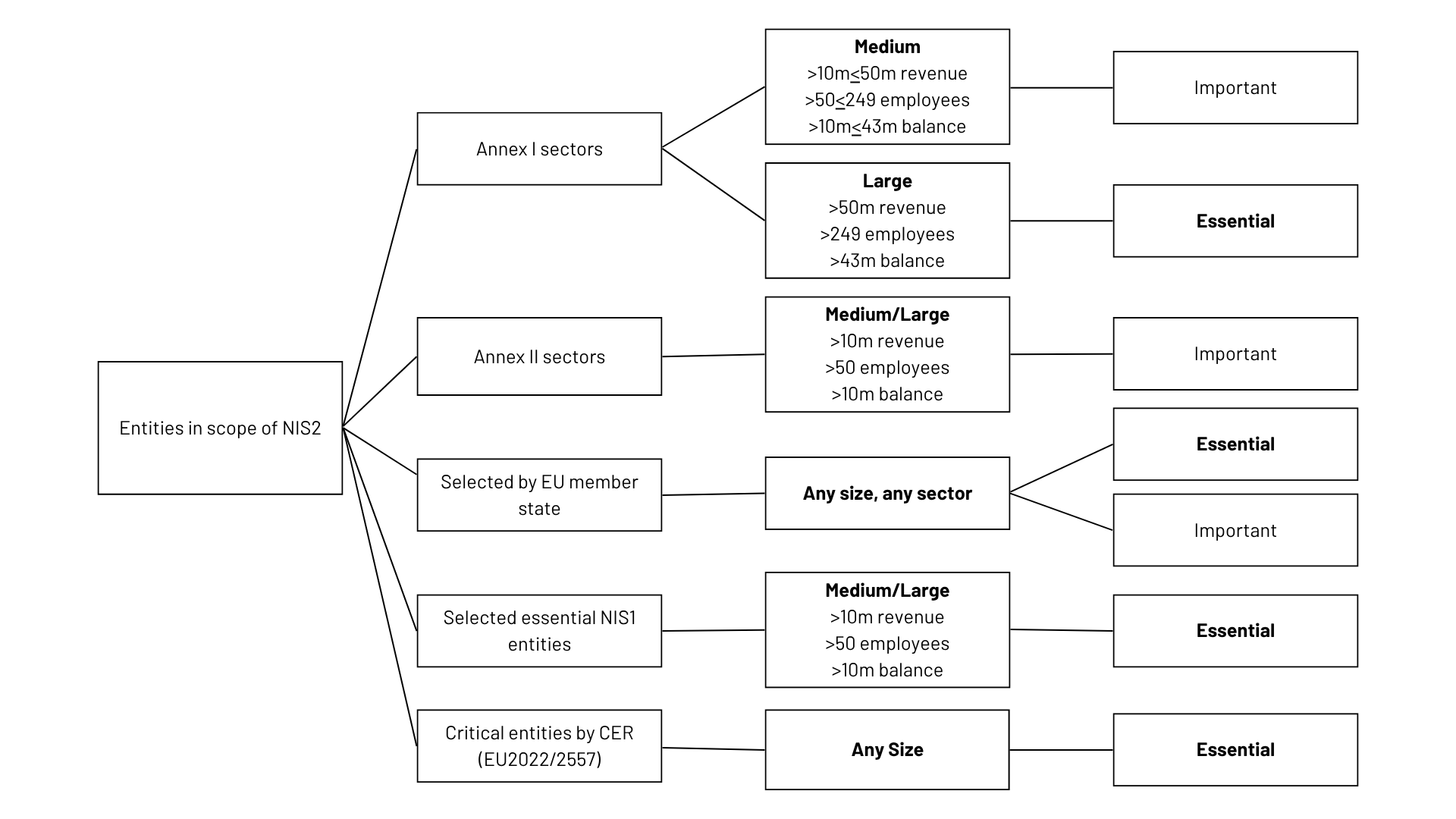
NIS2 establishes a tiered supervisory and enforcement regime, with "essential entities" facing a stronger supervisory regime than "important entities." However, both types can face significant consequences for non-compliance.
Supervision: What to Expect for Your OT/ICS Operations:
- Baseline for All Entities:
- Coordinated supervision with the entity’s legal representative.
- Includes both on-site and off-site inspections of your OT/ICS infrastructure and security practices.
- Authorities can request information and evidence of security policy implementation to assess compliance.
- Additional for Essential Entities:
- Regular and ad-hoc audits, including evidence collection for your OT security posture.
- Random, unplanned checks by authorities of your industrial systems.
Enforcement of Violations: Remediation and Directives for OT/ICS:
Should supervision reveal compliance violations, enforcement actions will be initiated.
- For All In-Scope Entities, Local Authorities Can:
- Issue warnings.
- Issue binding instructions to remediate incidents within a specified deadline (crucial for OT incident response).
- Order to cease infringing activities and make findings public, providing direct guidance.
- Order the implementation of security audit recommendations within a deadline.
- Impose administrative fines.
- Additional Enforcement for Essential Entities Includes:
- Temporary prohibition to exercise managerial function at the CEO or legal representative level (underscoring executive accountability for OT security).
- Designation of a monitoring officer to oversee compliance within your organization.
- Issuing binding instructions to prevent incidents, with strict deadlines for implementation and reporting.
Factors Influencing Enforcement Actions and Penalties:
When determining enforcement actions and penalties, authorities will consider:
- The severity of the infringement (for example, repeated violations, failure to notify or remediate significant OT incidents, obstruction of audits, providing false information).
- The duration of the infringement.
- Previous infringements.
- Material/non-material damage caused and users affected (for example, impact on critical services, public safety).
- Intent or negligence.
- Measures taken to prevent or mitigate damage.
- The level of cooperation with authorities.
Quick Checklist for First Operational Steps in OT/ICS:
In addition to the preceding action items, here is a quick checklist OT security teams can use to get started with NIS2.
- Asset detection and inventory: Are all relevant assets, including OS-based and embedded systems in OT, detected to a very high degree within an appropriate time frame?
- Policy and procedures: Are security policies documented, communicated, and regularly assessed for effectiveness across your OT environment?
- Incident reporting process: Is a clear, well-understood process in place to report potential significant incidents (as defined by NIS2) within your OT operations?
- Vulnerability and threat management: Have all in-scope OT assets been identified, are they continuously monitored, and are vulnerabilities and threats actively managed?
- Response capabilities: Is your entity capable of identifying, monitoring, alerting, and possessing the capabilities to respond effectively to OT threats?
- Ticketing and documentation: Is a ticketing system implemented to manage and document incident detection, triage, and response within your OT/ICS security workflow?
- Critical process security: Are critical OT processes and their associated assets known, documented, and protected by appropriate security measures?
- Supply chain risk management: Are supply chain risks for your OT/ICS components and services identified, and are mitigating measures actively in place?
- Reliable evidence: Can evidence from your OT security management system be relied upon for industrial assets during audits and assessments?
The Verve by Rockwell Automation Standard: Architecting OT/ICS Security for NIS2 Success
Verve by Rockwell Automation doesn't just help detect risks—it empowers teams to actively manage and remediate them across complex OT environments. This operational intelligence is key to achieving and sustaining NIS2 compliance.
What sets Verve apart is its ability to gather detailed, asset-related security information while also enabling remediation. That means you can move beyond simply identifying risks to taking informed action that closes gaps and strengthens defenses.
For many OT teams, resources are limited. Verve streamlines the process by collecting risk data from across the OT environment, analyzing it, and providing prioritized recommendations. A small expert team can then orchestrate a strategic response, while local operations teams remain in control of execution. This balance ensures organizations can improve security maturity without overwhelming staff or budgets.